With the latest massive ransomware attack that affected virtually the entirety of England’s National Heath Service system, physicians everywhere are reminded of the importance of patient privacy. Private practices may not always be the go-to target for ransomware attacks, but safeguards always need to exist and be up-to-date in order to protect privacy.
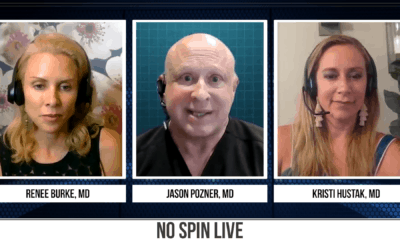
Board certified plastic surgeons of private practices discuss ransomware in the latest episde of No Spin Live, addressing why it’s important for them and their employees to be vigilant.
Thieving Patient Photos for Ransom
When it comes to plastic surgery – one of the more personal areas of medicine for patients, it’s crucial for many to retain anonymity before, during, and even after the process is complete. As can be seen with the recent NHS ransomware attack, large organizations are usually at risk most, but small practices are certainly not immune.
An event may occur as follows. An email may be sent to an account on an office server and if it is opened by the physician or staff, the entire server could be compromised. The differentiator between ransomware and typical malware is the software demands users on infected systems to pay a ransom in order for the insidious software to be lifted. This puts the user often in a precarious position – do we pay the ransom? Wipe the servers and restore from a backup (this is why backups are incredibly important!)? Or see what happens?
The fallout could be nothing, or it could break patient privacy laws and thus hurt the practice severely.
“I think it’s definitely something that’s important to us. Our patients HIPAA privacy, credit cards, photos – it’s super important that we keep that safe,” says board certified plastic surgeon Dr. Jason Pozner, who has a private practice in Florida. “But just like the government, we’re prone to hacking. It’s in our best interests to keep our patients safe, their information safe. Patients send us all photos from out of town and I try to make sure there’s no information on the patient in those emails, no faces that goes with bodies. It’s all very critical.”
Constant Vigilance from More than Just the Physician
While a physician or practice manager may be very fluent in preventing such attacks, it’s of extreme importance for all employees who engage in server systems to understand what to do with suspicious emails. One innocent click could cost a practice dearly.
“It’s not just us as the provider, it’s also everyone in our office – all of our staff, all of the people that come into contact with these patients and potentially interact with them electronically,” explains Dr. Jason Cooper, a board certified plastic surgeon who also has a private practice in Florida. “A lot of our staff are taking photos of patients – they’re the ones that take the pre and post operative photos and catalogue them. It’s just tantamount that everyone is on the same page and that there are policies and procedures internally for how these things are handled.”
To Pay or Not To Pay
If calamity transpires, it can be a difficult decision to give in to hacker demands, or spend considerable time and perform potentially risky maneuvers to undo the damage. Dr. Steven Teitelbaum, a board certified plastic surgeon in Los Angeles, had ransomware attack his own person computer and he had to make quick decisions as to how to rectify the issue before it could infect his practice’s system.
“I already had a ransomware attack on my personal computer and I’m as religious as possible about opening suspicious emails,” Dr. Teitelbaum explains. “I debated a lot whether to buy the bitcoins and do it, but finally what I did was gut my computer, threw out the hard drives, and put in hard drives and restored from a backup. That’s what I ended up doing, but thank God it didn’t get into the office system.”














Facebook
Twitter
Instagram
YouTube
RSS